Which type of cryptography uses two private keys?
Symmetric key cryptography uses a single secret key, while asymmetric key cryptography uses a pair of public and private keys. Public key cryptography was first devised as a means of exchanging a secret key securely by Diffie and Hellman.
Which type of cryptography uses two private keys?
Public Key Cryptography, or asymmetric cryptography, uses two keys to encrypt data. One is used for encryption, while the other key can decrypts the message.
Which type of cryptography uses only private keys symmetric public asymmetric private?
Asymmetric encryption is also called public key encryption, but it actually relies on a key pair. Two mathematically related keys, one called the public key and another called the private key, are generated to be used together. The private key is never shared; it is kept secret and is used only by its owner.
Which type of cryptography uses only public keys?
Public-key cryptography, or asymmetric cryptography, is a cryptographic system that uses pairs of keys.
What is private key in cryptography?
A private key is an extremely large number that is used in cryptography, similar to a password. Private keys are used to create digital signatures that can easily be verified, without revealing the private key. Private keys are also used in cryptocurrency transactions in order to show ownership of a blockchain address.
What is private key management in cryptography?
Private Key: this key is used to decrypt the data that it’s counterpart, the public key, has encrypted. This key must be safeguarded as it is the only key that can decrypt the encrypted data. Asymmetric keys are primarily used to secure data-in-motion.
Which type of cryptography uses to cryptography?
Three types of cryptography: secret-key, public key, and hash function. Types of stream ciphers. Feistel cipher. Use of the three cryptographic techniques for secure communication.
What is cryptography in e commerce?
Definition: Cryptography is associated with the process of converting ordinary plain text into unintelligible text and vice-versa. Cryptography is used in many applications like banking transactions cards, computer passwords, and e- commerce transactions.
What is traditional cryptography?
Traditional cryptography is based on the sender and receiver of a message knowing and using the same secret key: the sender uses the secret key to encrypt the message, and the receiver uses the same secret key to decrypt the message. Each person’s public key is published while the private key is kept secret.
What is public and private key in cryptography?
One key (public key) is used for encrypt the plain text to convert it into cipher text and another key (private key) is used by receiver to decrypt the cipher text to read the message.
Which type of cryptography is also called public key cryptography?
A Definition of Public Key Cryptography
Sometimes referred to as asymmetric cryptography, public key cryptography is a class of cryptographic protocols based on algorithms. This method of cryptography requires two separate keys, one that is private or secret, and one that is public.
Who keeps the private key in asymmetric key cryptography?
Explanation: The private key is kept only by the receiver of the message. Its aim is to make sure that only the intended receiver can decipher the message. 3. Which one of the following algorithm is not used in asymmetric-key cryptography?
What is public key cryptography example?
Example: Public keys of every user are present in the Public key Register. If B wants to send a confidential message to C, then B encrypt the message using C Public key. When C receives the message from B then C can decrypt it using its own Private key.
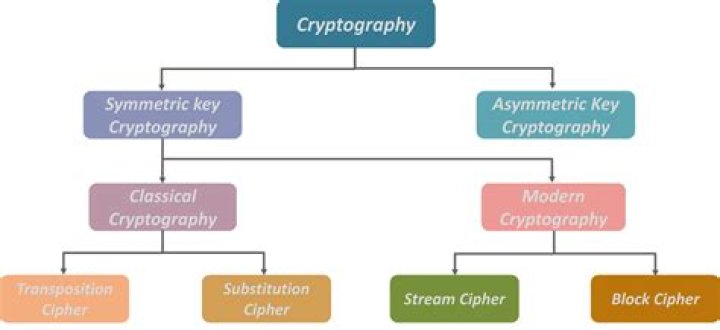
What are two types of cryptography?
Cryptography is broadly classified into two categories: Symmetric key Cryptography and Asymmetric key Cryptography (popularly known as public key cryptography).
How are public and private keys related?
Public and private keys form the basis for public key cryptography , also known as asymmetric cryptography. In public key cryptography, every public key matches to only one private key. Together, they are used to encrypt and decrypt messages.
Where is private key cryptography used?
A private key is also used in asymmetric cryptography, which is also known as public key cryptography. In this case, the private key refers to the secret key of a public key pair. In public key cryptography, the private key is used for encryption and digital signatures.
How many keys are used in private key cryptography?
For every user, there is 1 Private key and 1 Public key. The Private key is used to decrypt messages from other users. The Public key is used by everyone else to encrypt messages for that user. These keys are mathematically linked.