What type of file spreads malware?
Knowing PDF files, Word documents, and other document types are used to spread malware gives users and IT departments a better chance to combat the problem.
Which of the following is a type of malware that requires user interaction?
While many of these are closely related, each has some unique characteristics. Virus: a type of malware that is damaging to computers or files on a computer that is generally propagated through email or instant messages. It generally requires some user interaction to infect a computer.
What type of malware consists of a set of software tools used by an attacker to hide the actions or presence of other types of malicious software such as virus?
A rootkit is, as described by TechTarget, “a program or, more often, a collection of software tools that gives a threat actor remote access to and control over a computer or other system.” It gets its name because it’s a kit of tools that (generally illicitly) gain root access (administrator-level control, in Unix
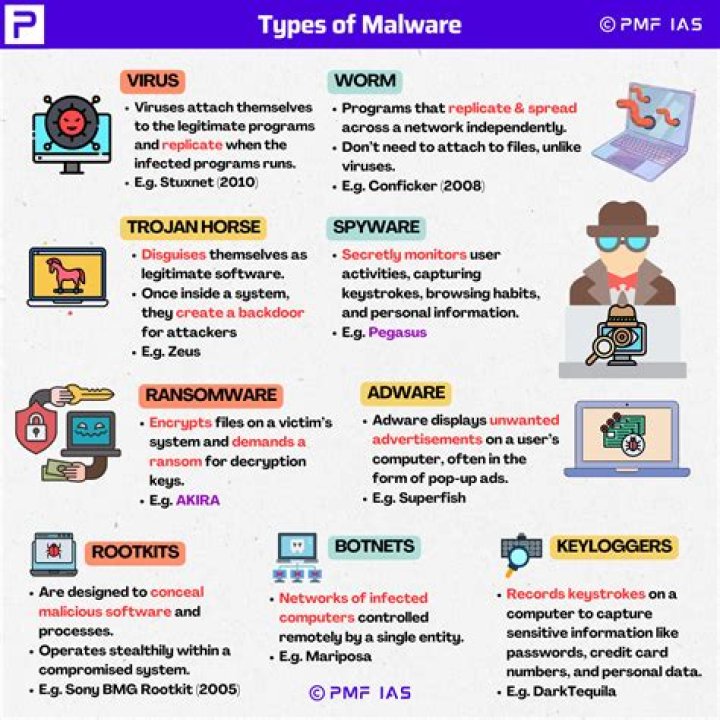
What are the 4 main types of malware?
The most common types of malware include viruses, worms, trojans, ransomware, bots or botnets, adware, spyware, rootkits, fileless malware, and malvertising.
How does malware spread?
Malware spreads in computer when you download or install an infected software. They also enter your computer through an email or a link. Once malware enters the computer, it attaches itself to different files and overwrites the data. Some malware are to be executed before it’s activated, but some spread immediately.
What is the type of malware that tricks users by making them believe?
Explanation: Scareware is part of a class of malicious software that includes rogue security software, ransomware and other scam software that tricks users into believing their computer is infected with a virus, then suggests that they download and pay for fake antivirus software to remove it.
What is malware and types of malware?
Malware is intrusive software that is designed to damage and destroy computers and computer systems. Malware is a contraction for “malicious software.” Examples of common malware includes viruses, worms, Trojan viruses, spyware, adware, and ransomware.
Which of the following provides the most protection against malware?
Using antivirus software is the best way to defend your computer against malicious code. If you think your computer is infected, run your antivirus software program. Ideally, your antivirus program will identify any malicious code on your computer and quarantine them so they no longer affect your system.
Which two types of malware can self-replicate and spread?
Virus vs Worm: Viruses are dormant until their host file is activated. Worms are malware that self-replicate & propagate independently once in the system.
Which malicious program monitors activities of users and also personal information of the users?
Spyware collects your personal information and passes it on to interested third parties without your knowledge or consent. Spyware is also known for installing Trojan viruses.
What is ransomware based on?
Ransomware is based on Option (D) Fear of losing important files. Explanation: Ransomware is a malware attack that makes use of the fear of the users. In such attacks, a victim’s file is infected via phishing or other spying methods and it restricts the victim’s access to their entire data.
Which type of malware is a set of software tools?
Rootkit. A set of software tools designed to allow an attacker to gain unauthorised access – often elevated (e.g. administrator level) access – to a computer without being detected.
Which type of malware is a set of software tools used by an attacker to hide the actions?
Trojan Horses
Trojan horse programs are malware that is disguised as legitimate software. A Trojan horse program will hide on your computer until it’s called upon. When activated, Trojans can allow threat actors to spy on you, steal your sensitive data, and gain backdoor access to your system.
Which type of malware is a set of software tools used by an attacker to hide the actions or presence?
What is a worm? A rootkit infects a computer and hides its presence from the operating system so that the rootkit files are not visible to the operating system.
What are the main types of spyware?
Spyware is mostly classified into four types: adware, system monitors, tracking including web tracking, and trojans; examples of other notorious types include digital rights management capabilities that “phone home”, keyloggers, rootkits, and web beacons.
Is sandboxing a type of malware?
Malware detection and sandboxing
Sandboxing is used to test code or applications that could be malicious before serving it up to critical devices. In cybersecurity, sandboxing is used as a method to test software which would end up being categorized as “safe” or “unsafe” after the test.
What is malware and its types PDF?
Malware stands for “Malicious Software” and it is designed to gain access or installed into the computer. without the consent of the user. They perform unwanted tasks in the host computer for the benefit of a third. party. There is a full range of malwares which can seriously degrade the performance of the host machine



