What are the five steps of opsec?
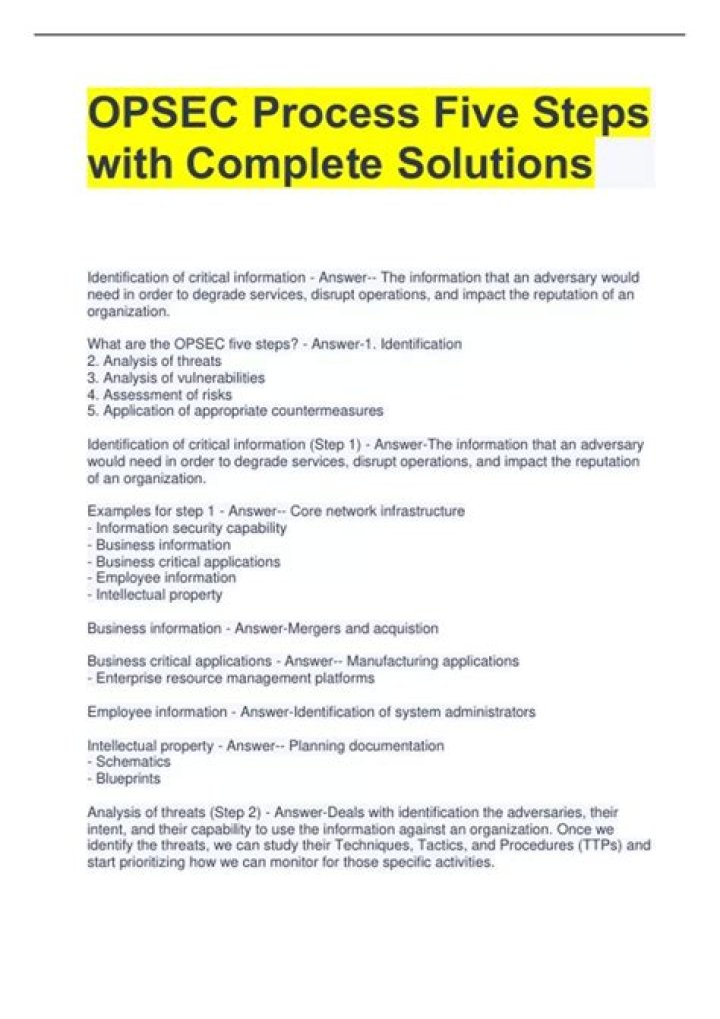
The OPSEC process is most effective when fully integrated into all planning and operational processes. The OPSEC process involves five steps: (1) identification of critical information, (2) analysis of threats, (3) analysis of vulnerabilities, (4) assessment of risk, and (5) application of appropriate countermeasures.
What are the OPSEC rules?
10 OPSEC Rules Every Military Spouse Should Know
Don’t Share Details of a Mission. Don’t Mention Your Military Spouse’s Specific Job Title. Don’t Post Location or Time of Unit Deployments. Don’t Post Details of Trainings. NEVER Post Casualty Information Before an Official Release. Avoid Gossip and Rumors.
Why is OPSEC important?
There are many reasons why having a healthy obsession with OPSEC is important. One of the biggest is protecting yourself from cyber-criminals, hackers and governments from obtaining data that can be used to disclose sensitive information about you, with doxxing the most common attack used to expose weaknesses in OPSEC.
These OPSEC officers perform a vital role in building an effective program, which helps protect the unit’s critical and sensitive information; and trains, informs and advises unit personnel on compliance with Army policies and procedures.
What is comsec and OPSEC?
OPSEC = Operational Security, COMSEC = Communications Security, INFOSEC = Information Security and PERSEC = Personal security. Information that shouldn’t be shared includes things like a soldier’s exact location overseas, info on troop movements, weapons systems etc.
“The objective of National Security Decision Directive 298 is to apply the operations security (OPSEC) process to promote operational effectiveness by helping prevent the inadvertent compromise of sensitive or classified U.S. Government activities, capabilities, or intentions.
What is Infosec army?
Information Security. The Information Security (INFOSEC) Program establishes policies, procedures, and requirements to protect classified and controlled unclassified information (CUI) that, if disclosed, could cause damage to national security.
What are some topics under Operations security?
Operations security best practices
Change-management processes. Companies must put change-management processes in place for employees to follow when adjustments are made to the network.Restrict device access. Implement least-privileged access. Deploy dual control. Implement automation. Craft a disaster recovery plan.
Yes, you can. Understand; however, that you are representing the brand by doing so, and that your actions on social media reflect that which you represent just as much as yourself. If you trash the brand you taint others perception of those wearing the same uniform so post wisely.
What is OPSEC and Persec?
OPSEC deals more with the day-to-day operations going on in the Marine Corps. This can be for anything from deployment dates to weapons serial numbers to troop movements. On the other hand, there is PERSEC. PERSEC deals more with each individual’s personal security and how they safeguard their own personal information.
What are the elements of threat?
Each of these elements has an essential role to play within a threat model.
Key stakeholders. The key stakeholders are the owners of the system. Assets. Security risks. Security threats and threat agents. Security vulnerabilities. Security controls and mitigations.
What is the greatest countermeasure?
What is the greatest countermeasure? There are security functions for which people are the best and sometimes the only countermeasure. The critical factor in the decision to use people, one that is their greatest attribute that can never be replaced, is their ability to exercise judgment.
Equipment designed to provide security to telecommunications by converting information to a form unintelligible to an unauthorized interceptor and, subsequently, by reconverting such information to its original form for authorized recipients; also, equipment designed specifically to aid in, or as an essential element
What is security in computing?
computer security, also called cybersecurity, the protection of computer systems and information from harm, theft, and unauthorized use. Computer hardware is typically protected by the same means used to protect other valuable or sensitive equipment—namely, serial numbers, doors and locks, and alarms.
How many steps are in OPSEC?
The OPSEC process involves five steps: (1) identification of critical information, (2) analysis of threats, (3) analysis of vulnerabilities, (4) assessment of risk, and (5) application of appropriate countermeasures.
What is OPSEC Level II?
A three (3) day Level II certification course designed to train appointed OPSECOfficers, Program Managers and relevant personnel in administering the organization’sOPSEC Program and advising the Commander in OPSEC matters.
Incorporate OPSEC policy into AR 380–49.