What are the 5 steps of OPSEC?
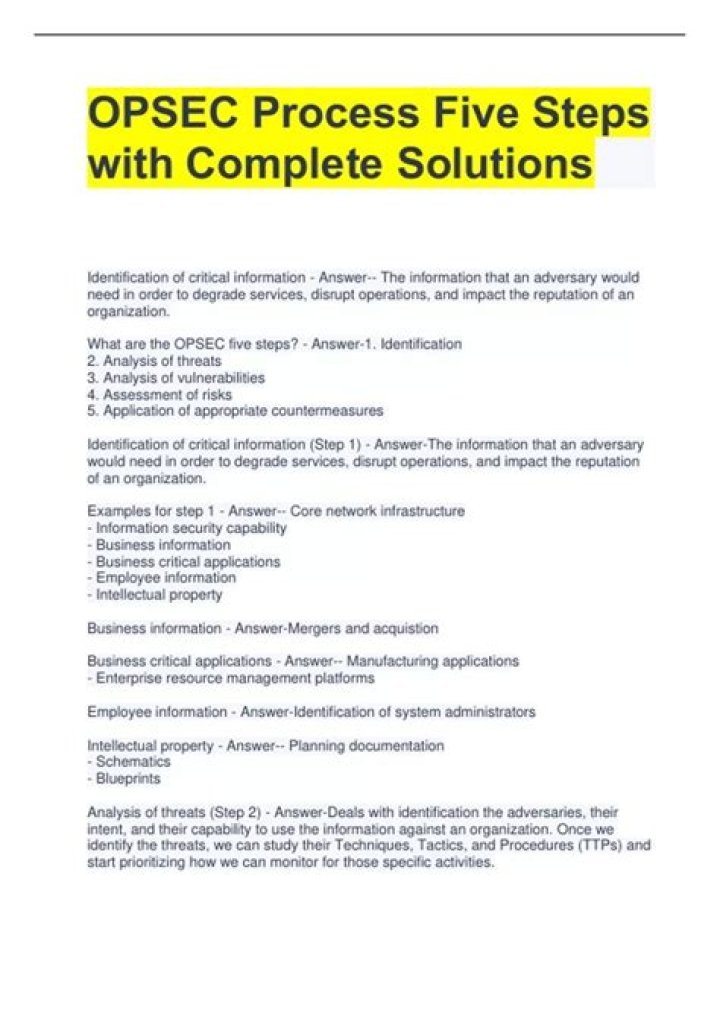
The OPSEC process is most effective when fully integrated into all planning and operational processes. The OPSEC process involves five steps: (1) identification of critical information, (2) analysis of threats, (3) analysis of vulnerabilities, (4) assessment of risk, and (5) application of appropriate countermeasures.
What are the OPSEC rules?
10 OPSEC Rules Every Military Spouse Should Know
Don’t Share Details of a Mission. Don’t Mention Your Military Spouse’s Specific Job Title. Don’t Post Location or Time of Unit Deployments. Don’t Post Details of Trainings. NEVER Post Casualty Information Before an Official Release. Avoid Gossip and Rumors.
What is OPSEC?
OPSEC (operations security) is a security and risk management process and strategy that classifies information, then determines what is required to protect sensitive information and prevent it from getting into the wrong hands.
Which step in the opsec process requires you to look at your operation through the eyes of the adversary? Identifying Critical Information requires you to look at your operation from both the friendly and adversary perspectives.
What are the elements of threat in OPSEC?
A threat is an adversary that has the capability + intent to take any actions detrimental to the success of DoD activities or operations. An adversary is an individual, group, organization, or government that must be denied critical information (DoDM 5205.02 “DoD Operations Security (OPSEC) Program Manual”).
The OPSEC process involves five steps: (1) identification of critical information, (2) analysis of threats, (3) analysis of vulnerabilities, (4) assessment of risk, and (5) application of appropriate countermeasures.
Can you post pictures in uniform?
Yes, you can. Understand; however, that you are representing the brand by doing so, and that your actions on social media reflect that which you represent just as much as yourself. If you trash the brand you taint others perception of those wearing the same uniform so post wisely.
What NSDD 298?
“The objective of National Security Decision Directive 298 is to apply the operations security (OPSEC) process to promote operational effectiveness by helping prevent the inadvertent compromise of sensitive or classified U.S. Government activities, capabilities, or intentions.
OPSEC = Operational Security, COMSEC = Communications Security, INFOSEC = Information Security and PERSEC = Personal security. Information that shouldn’t be shared includes things like a soldier’s exact location overseas, info on troop movements, weapons systems etc.
What is Infosec army?
Information Security. The Information Security (INFOSEC) Program establishes policies, procedures, and requirements to protect classified and controlled unclassified information (CUI) that, if disclosed, could cause damage to national security.
What are good OPSEC countermeasures?
OPSEC countermeasures may include, but are not limited to: modification of operational and administrative routines; the use of cover, concealment, deception; and other measures that degrade the adversary’s ability to exploit indicators of critical information.
What are elements of threat?
Each of these elements has an essential role to play within a threat model.
Key stakeholders. The key stakeholders are the owners of the system. Assets. Security risks. Security threats and threat agents. Security vulnerabilities. Security controls and mitigations.
Risk assessment is a decision-making step because it helps the decision maker prioritize and decide whether or not to assign a countermeasure to a vulnerability. The bottom line is to always weigh the cost of a countermeasure against the benefit. This completes the OPSEC Process Lesson.
What are the types of threat?
Threats can be classified into four different categories; direct, indirect, veiled, conditional.
What is the greatest countermeasure?
What is the greatest countermeasure? There are security functions for which people are the best and sometimes the only countermeasure. The critical factor in the decision to use people, one that is their greatest attribute that can never be replaced, is their ability to exercise judgment.
What is OPSEC designed to protect?
OPSEC, is an analytical process used to deny information generally unclassified from our adversaries, safeguards information concerning our intentions and capabilities by identifying, controlling and protecting indicators associated with our planning process or operations are exactly canceled you.
Terms in this set (10) OPSEC is: a process that is a systematic method used to identify, control, and protect critical information. understanding that protection of sensitive unclassified information is: the responsibility of al persons, including civilians and contractors.
Are like pieces of a puzzle an adversary?
Indicators are like pieces of a puzzle an adversary can use to reveal a picture of our operations. Indicators are like pieces of a puzzle an adversary can use to reveal a picture of our operations. This answer has been confirmed as correct and helpful.
What is OPSEC risk?
Operational security (OPSEC), also known as procedural security, is a risk management process that encourages managers to view operations from the perspective of an adversary in order to protect sensitive information from falling into the wrong hands.