social engineering is a whale phishing attack, check these out | Is phishing a social engineering attack?
Whaling is a highly targeted phishing attack – aimed at senior executives – masquerading as a legitimate email. Whaling is digitally enabled fraud through social engineering, designed to encourage victims to perform a secondary action, such as initiating a wire transfer of funds.
Is phishing a social engineering attack?
What is a phishing attack? Phishing is a form of social engineering. Phishing attacks use email or malicious websites to solicit personal information by posing as a trustworthy organization. When users respond with the requested information, attackers can use it to gain access to the accounts.
What is a whale phishing attack?
Whale phishing is a term used to describe a phishing attack that is specifically aimed at wealthy, powerful, or prominent individuals. Because of their status, if such a user becomes the victim of a phishing attack he can be considered a “big phish,” or, alternately, a “whale.”
What is whaling in social engineering?
Whaling is a common cyber attack that occurs when an attacker utilizes spear phishing methods to go after a large, high-profile target, such as the c-suite.
What type of phishing is whaling?
A whaling attack is a special form of spear phishing that targets specific high-ranking victims within a company. Spear phishing attacks can target any specific individual. Both types of attack generally require more time and effort on the part of the attacker than ordinary phishing attacks.
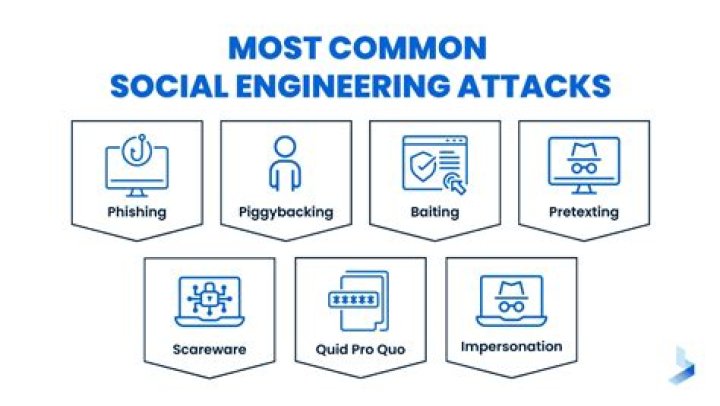
What are the 5 social engineering attacks?
The following are the five most common forms of digital social engineering assaults.
Baiting. As its name implies, baiting attacks use a false promise to pique a victim’s greed or curiosity. Scareware. Scareware involves victims being bombarded with false alarms and fictitious threats. Pretexting. Phishing. Spear phishing.
What are types of social engineering attacks?
10 Types of Social Engineering Attacks
Phishing. Whaling. Diversion Theft. Baiting. Honey Trap. Pretexting. SMS Phishing. Scareware.
What type of attack is phishing?
Phishing attacks are social engineering attacks, and they can have a great range of targets depending on the attacker. They could be generic scam emails looking for anyone with a PayPal account. Phishing can also be a targeted attack focused on a specific individual.
What three things can you do to prevent being a victim of a whale phishing attack?
Okay, so how can I prevent this from happening?
Educate your executives and employees. Then, train them. Flag emails outside of your network. Set up whaling prevention protocols. Invest in DLP software. Have employees make social media profiles private.
Which of the following is a way to protect against social engineering?
Which of the following is a way to protect against social engineering? Follow instructions given only by verified personnel. While on vacation, a coworker calls and asks you to access a site to review and approve a document that is hosted behind a DoD Public Key Infrastructure (PKI) protected webpage.
What is the difference between phishing Spearphishing and whaling?
The difference between whaling and spear phishing is that whaling exclusively targets high-ranking individuals within an organization, while spear phishing usually goes after a category of individuals with a lower profile.
What is phishing in cyber security?
Phishing attacks are the practice of sending fraudulent communications that appear to come from a reputable source. It is usually done through email. The goal is to steal sensitive data like credit card and login information, or to install malware on the victim’s machine.
What is clone phishing?
A clone phishing attack uses a legitimate or previously sent email that contains attachments or links. The clone is a near copy to the original where the attachments or links are replaced with malware or a virus.
What are some examples of phishing?
The Most Common Examples Of A Phishing Email
The Fake Invoice Scam. Let’s start with arguably the most popular phishing template out there – the fake invoice technique. Email Account Upgrade Scam. Advance-fee Scam. Google Docs Scam. PayPal Scam. Message From HR Scam. Dropbox Scam.
How many types of phishing are there?
With a better understanding of the twelve types of phishing attacks and how to identify them, organizations can protect their users and their data more effectively.
Email phishing. HTTPS phishing. Spear phishing. Whaling/CEO fraud. Vishing. Smishing. Angler phishing. Pharming.
What are the six types of social engineering?
6 Types of Social Engineering Attacks
Phishing. Phishing is a social engineering technique in which an attacker sends fraudulent emails, claiming to be from a reputable and trusted source. Vishing and Smishing. Pretexting. Baiting. Tailgating and Piggybacking. Quid Pro Quo.
Which is an example of social engineering?
9 most common examples of social engineering are:
Spear Phishing: email is used to carry out targeted attacks against individuals or businesses. Baiting: an online and physical social engineering attack that promises the victim a reward.
What social engineering means?
Social engineering is the act of exploiting human weaknesses to gain access to personal information and protected systems. Social engineering relies on manipulating individuals rather than hacking computer systems to penetrate a target’s account.



