How do passwords passed securely from server to client?
The only safe method for a website to transfer a password to the server is using HTTPS/SSL. If the connection itself is not encrypted, an ManInTheMiddle can modify or strip away any JavaScript sent to the client.
How do I securely transfer passwords?
When it comes to the secure communication of passwords, you have a few options.
Communicate passwords verbally, either in person or over the phone.Communicate passwords through encrypted emails. Sending passwords via unencrypted emails is never recommended. Send passwords in a password vault file such as KeePass.
How is password sent to server?
The password is sent as an encrypted form over the internet. Some of the best encryption technologies are SHA1, MD5 Hash etc. SHA1 returns a 160-bit hash(40 hexadecimal character) when this encryption technology is used while MD5 returns a 128-bit hash(32 hexadecimal character).
Is it safe to send password to server?
Never storing it, either. What nearly all (at least all good security login measures) do is to hash the password on the client machine, then send the hash code for comparison – NOT the password itself. The server stores the hash, and only compares the hash, it never sees the password.
Are password hash before sending to server?
Whether you send a plaintext password or a client-side hash of that password, you should hash that value at the server-side and compare that hash with the hash stored in the user record.
How is encryption done?
Encryption uses an algorithm to scramble, or encrypt, data and then uses a key for the receiving party to unscramble, or decrypt, the information. The message contained in an encrypted message is referred to as plaintext. In its encrypted, unreadable form it is referred to as ciphertext.
How do clients share passwords?
To protect your clients’ sensitive data, always use a password manager when sharing passwords with them. This way their data stays encrypted and secured against hackers. To make sharing process even easier, look for a guest feature in password manager!
Is it safe to send passwords over email?
Sending passwords through email is a common practice in the workplace which is a bad habit. If you are on the receiving end of a password transferred, be sure to change it immediately after logging into the desired system.
How do I send a password protected email?
Send messages & attachments confidentially
On your computer, go to Gmail.Click Compose.In the bottom right of the window, click Turn on confidential mode . Tip: If you’ve already turned on confidential mode for an email, go to the bottom of the email, then click Edit.Set an expiration date and passcode. Click Save.
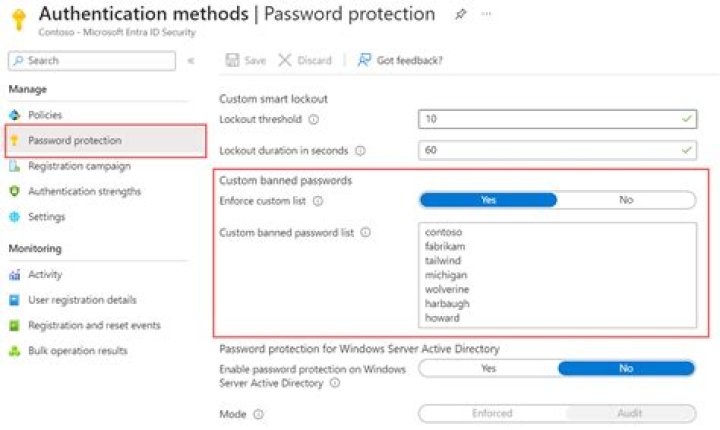
How are passwords encrypted in Active Directory?
Passwords stored in AD are hashed. Meaning that once the user creates a password, an algorithm transforms that password into an encrypted output known as a “hash”. Hashes are of fixed size so passwords of different lengths will have the same number of characters.
Where are passwords stored on domain controller?
On domain members and workstations, local user account password hashes are stored in a local Security Account Manager (SAM) Database located in the registry. They are encrypted using the same encryption and hashing algorithms as Active Directory.
How does password encryption work?
But put plainly, password encryption works by putting your original word through a series of scrambling steps. Symmetric key: Your system has a key for encryption/decryption. Move your password through this key to scramble it, and push it back through the key to make it readable once more.
Does HTTP send passwords in clear text?
When using standard HTTP, all the information is sent in clear text. Normally this is not be a big deal if you are just browsing regular websites and no sensitive data such as passwords or credit card information are being used.
Is plain text password safe over HTTPS?
It is safe. That’s how the entire web works. All passwords in forms are always sent in plain text, so its up to HTTPS to secure it.
How are passwords stored in database?
The password entered by user is concatenated with a random generated salt as well as a static salt. The concatenated string is passed as the input of hashing function. The result obtained is stored in database. Dynamic salt is required to be stored in the database since it is different for different users.
Which of the following is an efficient way to securely store passwords?
Some basic protocols you can follow to secure your users are: Use HTTPS / SSL on any page that a user enters their password, so that the data between the user’s browser and your server is encrypted. This ensures that no sniffer on the LAN or ISP can read the password. Lock a user after multiple failed login attempts.
What is salting a password?
While it may seem like a safe way to store passwords, there is a problem. If two passwords are the same, their hash is identical, which makes it easier to crack. This is where password salting comes in. A password salt is a random bit of data added to the password before it’s run through the hashing algorithm.
Why are hashes salted?
Recap. A cryptographic salt is made up of random bits added to each password instance before its hashing. Salts create unique passwords even in the instance of two users choosing the same passwords. Salts help us mitigate hash table attacks by forcing attackers to re-compute them using the salts for each user.



